In recent months, eSentire's Threat Response Unit (TRU) has observed an increased use of Microsoft Teams phishing involving IT/helpdesk impersonation. To help organizations identify and guard against this threat, we are sharing a Microsoft Sentinel query and mitigation guidance.
Microsoft Teams allows organizations to easily collaborate and communicate with each other. It includes a built-in feature that allows users to share their screens and give control to their IT/helpdesk team when needed. While this feature is valuable for troubleshooting, it also presents a risk to users.
In a typical attack scenario, the threat actor persuades the target to download remote monitoring and management (RMM) tools or grant control during chat/call sessions leading to the installation of additional malicious applications. In some cases, victims were contacted by fake IT/helpdesk staff following an increased volume of email spam.
This technique, known as email bombing, adds urgency and relevance to the social engineering attack. TRU discussed email bombing in our July 2025 TRU Intelligence Briefing.
Our team has observed a common pattern in this new phishing campaign method, which involves using trial Microsoft domains that have not been verified or connected.
While it is important to periodically review external domains users interact with, the domains we have observed typically follow the format: <userName>@<domainName>.onmicrosoft.com. This format allows threat actors to use domain names that impersonate IT/helpdesk departments and create generic helpdesk usernames.
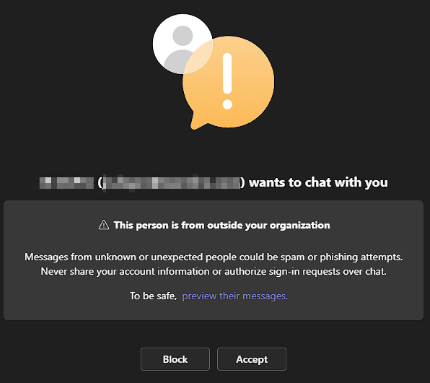
Threat actors begin by creating a temporary domain name and user that typically includes keywords such as "helpdesk," "IT," or "Support", etc. This pattern is often repeated in the username creation. The next stage of the attack involves messaging users of a targeted organization via Microsoft Teams.
Although users receive a prompt indicating an external message is received, the use of keywords like "IT", "Helpdesk", and "Support" may lead them to believe they are having a safe interaction with their internal team.
At this stage, the threat actors can persuade the user to either download an attachment or share their screen and give control which will lead to a compromise account / endpoint.
Recommendations from our Threat Response Unit (TRU)
- Regularly conduct Phishing and Security Awareness Training (PSAT) with your employees and incorporate this phishing technique during your training. This will help users identify and report this threat.
- Block external domains / users, unless there is a business requirement. IT Admins can implement a block/allow list of domains and users. See IT Admins - Manage external meetings and chat with people and organizations using Microsoft identities - Microsoft Teams
- Ensure all your endpoints have an Endpoint Detection and Response (EDR) solution and a Next-Gen AV solution installed to identify malicious apps / script execution.
Appendix
Microsoft Sentinel Threat Hunt Query
Use the following Microsoft Sentinel threat hunt query to identify Microsoft Teams messages that have IT/helpdesk keywords in the User Name, Chat Name, or Domain Name fields. This requires ingesting Office Activity logs using the Data Connector: Microsoft 365 (formerly, Office 365), Data Type: Microsoft 365 (formerly, Office 365).
See Connect Data Sources to Microsoft Sentinel Using Data Connectors for more information.
OfficeActivity
| where RecordType == "MicrosoftTeams" and CommunicationType == "OneOnOne"
| where isnotempty(UserId)
| extend User_Domain = tostring(tolower(split(UserId, "@", 1)[0]))
| where User_Domain contains ".onmicrosoft.com"
| where (tolower(UserId) matches regex @"(help|desk|support|^tech|tech$|tech\s|assistance|troubleshoot|admin|^it|it$|it\s)" or User_Domain matches regex @"(help|desk|support|^tech|tech$|tech\s|assistance|troubleshoot|admin|^it|it$|it\s)") or (tolower(UserId) matches regex @"(help|desk|support|^tech|tech$|tech\s|assistance|troubleshoot|admin|^it|it$|it\s)" and tolower(ChatName) matches regex @"(help|desk|support|tech|assistance|troubleshoot|admin|it)")
| summarize TimeGenerated = max(TimeGenerated) by ChatThreadId, UserId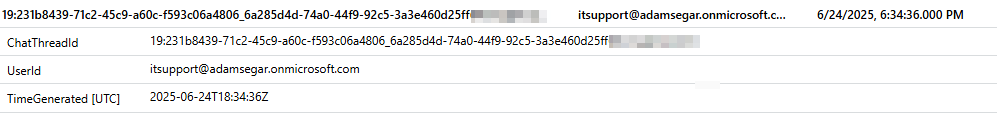
Sample of Malicious Users/Addresses
- fenixkonor@Administratoritdep[.]onmicrosoft[.]com
- tech@mintyfreshwave[.]com
- helpdeskmanager@arellano[.]pe
- cybersecurityhelpdesk[.]onmicrosoft[.]com
- supportbot@supportteamits[.]onmicrosoft[.]com
To learn how eSentire can help you find exposures and defend your organization, connect with an eSentire Security Specialist now.
GET STARTEDABOUT ESENTIRE’S THREAT RESPONSE UNIT (TRU)
The eSentire Threat Response Unit (TRU) is an industry-leading threat research team committed to helping your organization become more resilient. TRU is an elite team of threat hunters and researchers that supports our 24/7 Security Operations Centers (SOCs), builds threat detection models across the eSentire XDR Cloud Platform, and works as an extension of your security team to continuously improve our Managed Detection and Response service. By providing complete visibility across your attack surface and performing global threat sweeps and proactive hypothesis-driven threat hunts augmented by original threat research, we are laser-focused on defending your organization against known and unknown threats.