March 4, 2026 – Today, Microsoft announced they took action to disrupt and coordinate seizure of infrastructure associated with Tycoon 2FA Phishing-as-a-Service (PhaaS). eSentire is proud to have assisted with this effort to target and interrupt the operations of a key player in the cybercrime service landscape.
A Widespread, Pervasive Threat
eSentire’s security research team, the Threat Response Unit (TRU), has tracked Tycoon 2FA since it emerged in 2023. The platform offers sophisticated adversary-in-the-middle phishing capabilities, including Multi-Factor Authentication (MFA) code interception, session cookie capture and robust anti-analysis techniques described in our 2025 blog.
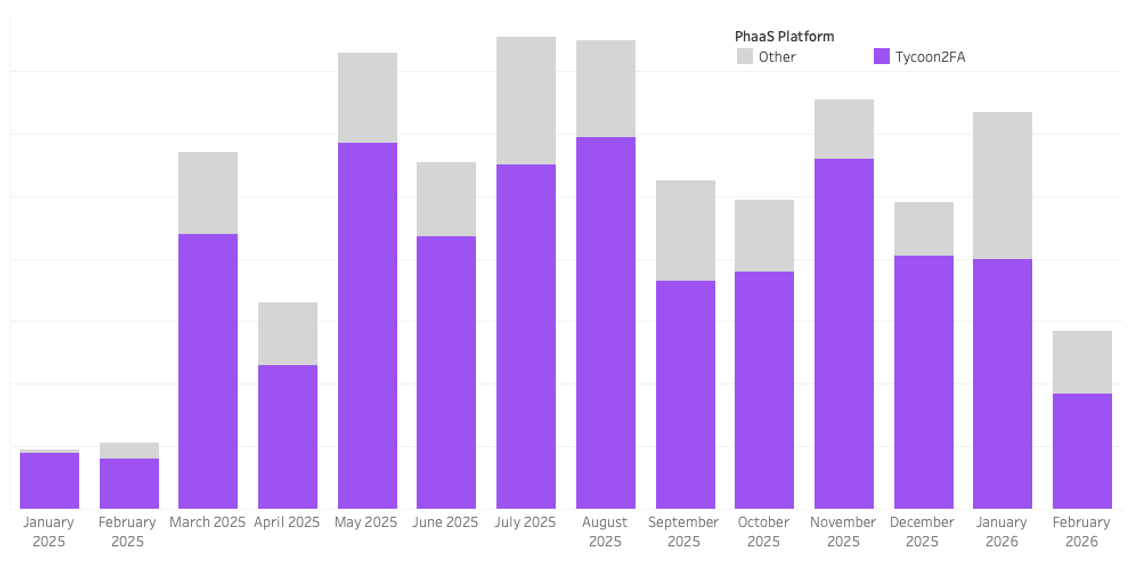
These capabilities have enabled threat actors to conduct sophisticated, pervasive credential phishing attacks over the past several years. Last year, TRU traced 32% of all security incidents to the platform, making it the leading source of identity compromise across eSentire’s global customer base.
Our analysis of Tycoon 2FA and their users shows the platform is a key conduit for Business Email Compromise (BEC) fraud. Our case data indicated threat actors began exploiting employee business accounts on average within 14 minutes of the initial account compromise.
In 2025, TRU identified Tycoon 2FA as the initial access vector in approximately 18% of disrupted intrusions consistent with BEC tactics. In one case, eSentire's Digital Forensics and Incident Response team was engaged by a non-customer to investigate a multi-million dollar Business Email Compromise incident. TRU traced the origins of this attack to a Tycoon 2FA phishing event nearly a month prior.
This operation disrupted a significant threat that has enabled cybercriminals to bypass multi-factor authentication and compromise organizations worldwide since it first appeared on the cybercrime scene in 2023. While threat actors will adapt and new challenges will emerge, each successful disruption strengthens our collective defenses and raises the bar for cybercriminals.
While this takedown represents a meaningful victory, our work is far from over. Threat actors will continue to evolve their tactics, and new phishing-as-a-service platforms will emerge.
eSentire remains committed to:
- Proactive threat hunting and early detection of emerging PhaaS infrastructure
- Sharing threat intelligence with law enforcement and industry partners
- Protecting our clients through 24/7 monitoring and rapid response
- Advancing the security community's collective defense capabilities
We encourage all organizations to remain vigilant, implement defense-in-depth strategies, and ensure employees are trained to recognize sophisticated phishing attempts—even those designed to bypass MFA.
Detection Guidance and Hunting Query
Detection Guidance
Monitor Entra ID sign-in logs for:
- User-Agent strings containing the string “axios”
- Authentication to Application ID 4765445b-32c6-49b0-83e6-1d93765276ca
- Audit connections from the ASNs historically linked to Tycoon 2FA authentication events (AS29802, AS9009, AS215540).
- See previous guidance here
- Unusual authentication patterns (geography, time, device)
Advanced Hunting Query for Microsoft Defender and Sentinel
Important Info: To run the query in Advance Hunting within the Defender Portal, you must have completed the Onboarding Microsoft Sentinel to Defender Portal, and have both tables ingested to Sentinel. Ref: https://learn.microsoft.com/en-us/unified-secops/microsoft-sentinel-onboard
Further Reading:
- https://www.esentire.com/security-advisories/network-infrastructure-abused-in-ongoing-phishing-attacks
- https://www.esentire.com/blog/phish-chips-serving-up-tycoon-2fas-secrets
To learn how eSentire can help you find exposures and defend your organization, connect with an eSentire Security Specialist now.
GET STARTEDABOUT THE AUTHOR

Spence Hutchinson Senior Manager, Threat Intelligence Research
As part of the broader Threat Response Unit, Spence is responsible for monitoring the evolving threat landscape and collaborating with TRU members to respond to ongoing threats. Throughout his tenure at eSentire, he has progressed through various analytical, training, and leadership roles, bringing extensive experience in threat research and security operations to the organization.