
Watch this video to learn how Quarles & Brady leverages eSentire MDR for Microsoft to protect their Microsoft ecosystem.
Watch this video to learn how Quarles & Brady leverages eSentire MDR for Microsoft to protect their Microsoft ecosystem.

Elemica partnered with eSentire for 24/7 Managed Detection & Response instead of building & staffing their own Security Operations Center (SOC).
Elemica partnered with eSentire for 24/7 Managed Detection & Response instead of building & staffing their own Security Operations Center (SOC).

Learn how to link Okta within the Atlas Platform for identity visibility.
Learn how to link Okta within the Atlas Platform for identity visibility.

Watch this video to learn about the role that the Blue Team plays in setting up, deploying, and maintaining your SIEM as part of our MDR for Log service.
Watch this video to learn about the role that the Blue Team plays in setting up, deploying, and maintaining your SIEM as part of our MDR for Log service.

Learn how eSentire MDR for Log delivers critical visibility across hybrid and multi-cloud environments to drive deeper threat investigations and rapid threat containment.
Learn how eSentire MDR for Log delivers critical visibility across hybrid and multi-cloud environments to drive deeper threat investigations and rapid threat containment.
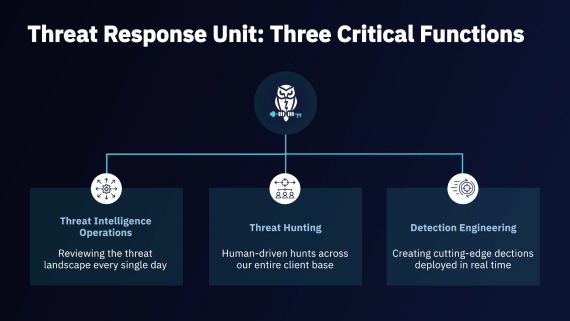
See how our Threat Response Unit (TRU) performs proactive threat hunting, conducts original threat research and develops new threat detection rules that are deployed to customers.
See how our Threat Response Unit (TRU) performs proactive threat hunting, conducts original threat research and develops new threat detection rules that are deployed to customers.

Watch this video to learn why you can count on our certified SIEM experts to set up, deploy, and maintain your SIEM better than any other in the industry.
Watch this video to learn why you can count on our certified SIEM experts to set up, deploy, and maintain your SIEM better than any other in the industry.

Learn how enhancing eSentire MDR with log telemetry helps deepen threat investigation and provide complete response across your multi-cloud and hybrid environments.
Learn how enhancing eSentire MDR with log telemetry helps deepen threat investigation and provide complete response across your multi-cloud and hybrid environments.

Review the Kaseya VSA supply chain attacks and see how eSentire’s Security Operations Center & Threat Response Unit were able to quickly respond on our customer’s behalf and notify Kaseya of the breaches.
Review the Kaseya VSA supply chain attacks and see how eSentire’s Security Operations Center & Threat Response Unit were able to quickly respond on our customer’s behalf and notify Kaseya of the breaches.

Learn how the eSentire Threat Response Unit (TRU) proactively detected and contained ProxyShell vulnerabilities in customer environments.
Learn how the eSentire Threat Response Unit (TRU) proactively detected and contained ProxyShell vulnerabilities in customer environments.

See how the eSentire Threat Response Unit (TRU) led threat hunts to proactively identify customers vulnerable to the Log4j zero-day.
See how the eSentire Threat Response Unit (TRU) led threat hunts to proactively identify customers vulnerable to the Log4j zero-day.

See how our Threat Response Unit (TRU) proactively detects and contains browser-basedcyberattacks that leverage Socgholish malware.
See how our Threat Response Unit (TRU) proactively detects and contains browser-basedcyberattacks that leverage Socgholish malware.