In 2025, identity-related cybercrime scaled rapidly with the expansion of "as-a-Service" models. Offering subscription-based access to an underground marketplace trading in digital identities, Phishing-as-a-Service (PhaaS) platforms enabled easier and more convenient account compromise than ever before. Unsurprisingly, account compromise attacks accounted for 50% of all threat cases investigated by the eSentire Threat Response Unit (TRU) against our global customer base.
In tandem, social engineering techniques hit new heights: according to the latest threat and incident data compiled in TRU's 2025 Year in Review Report, email bombing and IT impersonation surged 14x year-over-year.
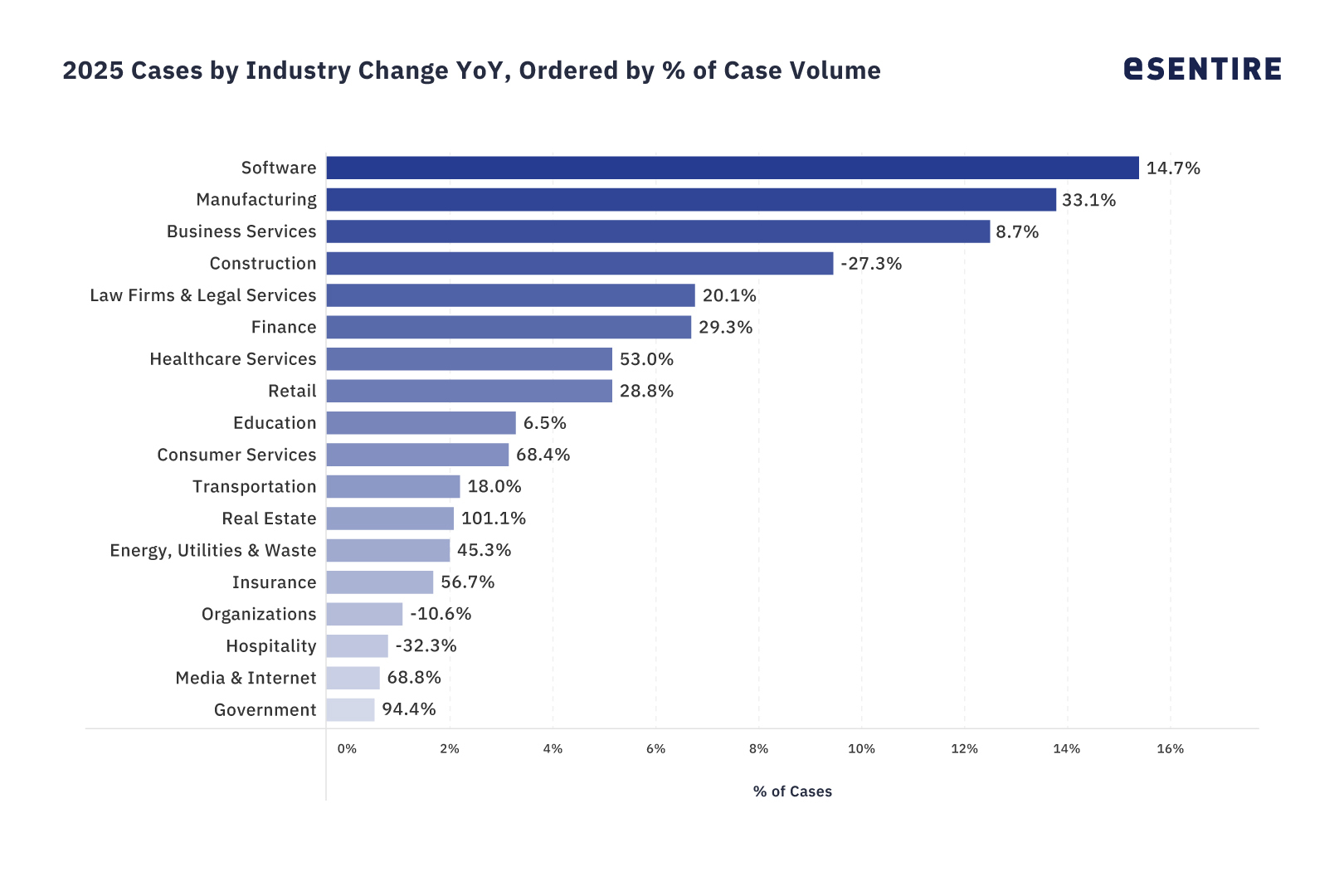
TRU's analysis revealed five industries bore the brunt of this onslaught: Software, Manufacturing, Business Services, Legal, and Construction. These sectors faced the highest concentration of sophisticated attacks throughout 2025.
The new reality is clear: for most organizations, the speed and number of cyberattacks drastically exceed the capabilities of traditional defense. Therefore, your organization's 24/7 threat detection and response capabilities must adapt accordingly to the rapid escalation and industrialization of cyberattacks.
This blog features critical insights from TRU's 2025 Year in Review report, highlighting why these five industries became prime targets and the specialized tactics malicious operators deployed against each sector.
Software's Perfect Storm: IP Value, Cloud Access, and Supply Chain Vulnerabilities
The Software industry emerged as the most frequently targeted sector among eSentire's customer base in 2025, experiencing a nearly 15% year-over-year increase in threat cases. This significant uptick can be attributed to several factors that make Software companies particularly attractive targets:
- Valuable intellectual property that can be monetized or leveraged for competitive advantage.
- Extensive access to cloud infrastructure with potential for lateral movement.
- Opportunity for supply chain attacks that can compromise thousands of downstream customers in a single breach.
The continued targeting of software companies underscores the strategic value threat actors place on compromising organizations that serve as distribution points for malicious code or access to broader networks.
Our Recommendations:
- Strengthen Cloud Security Posture: Implement continuous monitoring of cloud environments that host intellectual property and sensitive code repositories. Consider cloud-native security controls that can detect unusual access patterns or unauthorized configuration changes.
- Enhance Software Supply Chain Security: Adopt security practices that verify code integrity throughout the development lifecycle. Implement automated checks for third-party components and libraries to prevent supply chain compromises.
Manufacturing's 33% Threat Surge: Where OT Vulnerabilities Meet Ransomware Economics
Manufacturing faces significant cybersecurity challenges, recording a 33% year-over-year increase in security incidents and ranking second among all industries for threat frequency. TRU's research identified two critical vulnerabilities driving this concentrated attention:
- Persistent vulnerabilities in operational technology (OT) systems that are often difficult to patch without disrupting production.
- The sector's susceptibility to ransomware attacks, due to extraordinarily high downtime costs, makes Manufacturing organizations more likely to pay ransoms.
Manufacturing's growing digitalization has expanded the attack surface, thereby creating more entry points for threat actors, while older systems often remain in place without adequate security controls.
Our Recommendations:
- Bridge IT/OT Security Gaps: Develop unified security visibility across both information technology and operational technology environments while respecting the unique requirements of manufacturing systems.
- Implement Resilience Measures against Ransomware: Focus on backup strategies and recovery processes tailored to manufacturing environments, where downtime costs are exceptionally high.
Business Services: How MSPs Became the Ultimate Multiplier for Threat Actors
Organizations in the Business Services industry experienced the third-highest number of cases investigated and resolved by TRU in 2025, with an 8% year-over-year increase. Managed Service Providers (MSPs) in particular have become priority targets for sophisticated threat actors who recognize their value as a centralized attack vector due to the following factors:
- Compromising a single MSP can provide access to dozens or even hundreds of downstream customers.
- The trusted relationship between service providers and clients creates opportunities for supply chain attacks, leading to 85% intrusion rates in 2025.
- Access to credentials that have elevated privileges across multiple downstream client networks.
This targeting pattern aligns with the broader trend of threat actors seeking operational efficiency by maximizing impact through strategic target selection.
Our Recommendations:
- Segment Client Environments: Implement strict access controls between client environments to prevent the compromise of one client from easily spreading to others under management.
- Monitor for Unusual Authentication Patterns: Implement security monitoring to detect unusual access patterns across managed environments, particularly after-hours access or access from unusual locations.
Building Better Defenses: The Construction Industry's Security Turnaround
TRU reported that Construction industry customers experienced a 27% decrease in cyber incidents. However, when threat actors did target this sector, they primarily chose to do so through identity-related threats, including:
- Business Email Compromise (BEC)
- Account takeovers
- Credential phishing campaigns
The significant reduction in incidents can be attributed to a broader decline in BEC attacks across the construction industry, providing a much-needed reprieve for many companies in this sector.
Our Recommendations:
- Strengthen Identity Verification Processes: Continue improving verification mechanisms for financial transactions and communications to prevent BEC attacks that target construction payment workflows.
- Implement Project-Specific Security Controls: Tailor security measures to the specific requirements of individual construction projects, recognizing that different clients and projects may have different security needs.
Improved Security Intelligence: Legal Sector Maps Shifting Cybercriminal Strategies
Customers in the Legal industry saw a 20% rise in threat cases year-over-year, and they also experienced a notable shift in attack methodology.
The most significant trend observed was a dramatic increase in multi-stage attacks beginning with Email Bombing, followed by IT Help Desk Impersonation, a tactic which involves threat actors flooding email inboxes with spam before posing as IT support staff to "resolve" the manufactured crisis. In response, the victim grants remote access, which is then used to deploy ransomware or conduct other malicious actions.
In 2025, this tactic was responsible for 60 security incidents investigated and resolved by TRU. This evolution demonstrates how threat actors continuously refine their techniques, using initial email bombing to overwhelm targets' inboxes before following up with convincing IT support impersonation to exploit the resulting confusion.
Our Recommendations
- Establish Email Disruption Protocols: Develop clear procedures for staff to follow during potential email bombing attacks, including alternative communication channels and authentication procedures.
- Create IT Support Authentication Processes: Implement verification procedures to help employees distinguish legitimate IT support requests from impersonation attempts, especially after communication disruptions.
Adapting to the New Threat Reality
The 2025 threat landscape revealed the full industrialization of cybercrime, with PhaaS platforms and sophisticated social engineering creating new challenges across industries. While each sector faced unique threats, organizations that prioritized identity security and enhanced detection capabilities demonstrated significantly better outcomes. As attack sophistication continues to outpace traditional defenses, security teams must pivot toward more proactive, intelligence-driven approaches tailored to their specific industry risks.
For a deeper analysis of these trends and strategic guidance on strengthening your organization's security posture, access the complete 2025 Year in Review, 2026 Threat Landscape Outlook Report.
To learn how eSentire can help you find exposures and defend your organization, connect with an eSentire Security Specialist now.
GET STARTEDABOUT THE AUTHOR

Cassandra Knapp Senior Director, Growth Marketing
Cassandra Knapp has over 15 years of experience in marketing and currently serves as the Senior Director, Growth Marketing at eSentire. In her 8-year tenure at eSentire, her expertise in cybersecurity marketing has enhanced the prominence of core products such as Managed Detection and Response, Digital Forensics and Incident Response, and Exposure Management. Cassandra holds a Master of Arts in Advertising from Michigan State University and an Honour Bachelor of Commerce focusing on Marketing from McMaster University.