What Happened?
eSentire's Security Advisory on this incident can be found here: https://www.esentire.com/security-advisories/axios-npm-packages-compromised
Late in the evening on Monday, March 30th (early morning March 31st UTC) Axios, one of the most popular JavaScript HTTP client libraries became the target of a supply chain attack when two backdoored versions ([email protected] and [email protected]) were published using a compromised maintainer account.
These versions were live for approximately a three-hour window and introduced a malicious dependency that silently installed a RAT on Windows, macOS and Linux hosts. The campaign has been attributed to a North Korean threat actor UNC1069 (also tracked as Sapphire Sleet, STARDUST CHOLLIMA).
The tampered package was identified by Elastic Security Labs who notified the community and later released detailed analysis of the infection chain and payloads which have now been widely dissected and reported.
When the compromised packages went live, eSentire's Security Operations Center (SOC) began responding to malware cases across Windows and macOS hosts. Following the public disclosure of the compromise by Elastic Security Labs, eSentire's Threat Response Unit (TRU) validated existing cases and initiated an in-depth threat hunt across all customers.
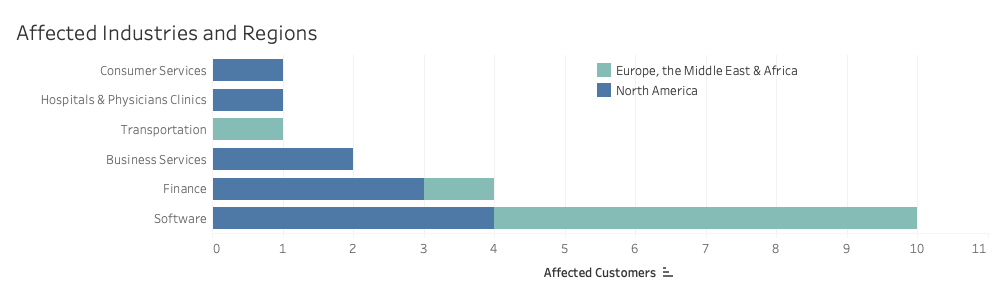
We identified a total of 19 affected customers, primarily within the software industry across North America and EMEA.
What is Axios?
Axios is a popular, open-source promise-based HTTP client for JavaScript. It simplifies making HTTP requests (like GET, POST, PUT, DELETE, etc.) in both the browser and Node.js environments using the same codebase. It is a popular choice for developers over the native fetch() API.
Axios has over 100,000,000 weekly downloads and 174,121 dependent packages making it one of the most popular packages available.
Payload Delivery
The tampered versions of Axios added a dependency for [email protected], which triggers a postinstall hook that executes the first stage payload (setup.js, tracked as SILKBELL). SILKBELL subsequently connects to attacker-controlled infrastructure to download the cross-platform RAT, which Mandiant tracks as WAVESHAPER.V2 and CrowdStrike tracks as ZshBucket.
Regardless of the operating system, the malware beacons to the Command and Control (C2) endpoint over port 8000 at 60-second intervals using a spoofed Internet Explorer 8 User-Agent string.
A brief summary of the platform-specific execution behavior and RAT functions are included below:
- Windows: The dropper locates the native powershell.exe binary and copies it to %PROGRAMDATA%\wt.exe so that it masquerades as Windows Terminal to evade Endpoint Detection and Response (EDR) tools. It uses a hidden VBScript to download a PowerShell payload to the user's temporary directory (%TEMP%\6202033.ps1) and executes it using the disguised wt.exe with execution policy bypass flags. The malware establishes persistence by creating a hidden batch file (system.bat) and adding a registry run key (HKCU:\Software\Microsoft\Windows\CurrentVersion\Run) under the name MicrosoftUpdate.
- macOS: The script uses AppleScript and curl to fetch a native C++ Mach-O binary payload. It saves this binary to /Library/Caches/com.apple.act.mond to blend in as a legitimate Apple system cache daemon. The malware then modifies the file permissions to make it executable and launches it silently in the background using zsh
- Linux: The malware uses a shell command and curl to download a Python backdoor to /tmp/ld.py. It then launches the payload using nohup python3, which allows it to run silently in the background and detach from the current process tree
Note: Across all three operating systems, the malware connects to the exact same Command and Control (C2) endpoint but sends a platform-specific POST body (product1 for Windows, product0 for macOS, and product2 for Linux) so the server knows which payload to return
A summary of the command and control (C2) response options for the malware include:
Timeline and Discovery
The earliest known infection in our telemetry occurred minutes after publication of the malicious [email protected] release.
A high-level timeline of events is shown below:
2026-03-31 00:21 UTC – Malicious [email protected] published
2026-03-31 00:25 UTC – Earliest known infection observed
2026-03-31 01:00 UTC – [email protected] published
2026-03-31 01:46 UTC – Joe Desimone Tweet notifying community
2026-03-31 01:50 UTC – Elastic team files GitHub security advisory
2026-03-31 03:25 UTC – Affected packages removed
While discussion of a possible Axios supply chain compromise played out, our SOC was actively responding to detection events for activity associated with the payload delivery. For Windows hosts, the suspicious renamed PowerShell processes attempting to masquerade as wt.exe on Windows hosts was consistently flagged while on macOS detections for suspicious file ingress and the Mach-O binary (/Library/Caches/com.apple.act.mond) were also identified and triaged accordingly. The Linux payload was not observed on monitored hosts.
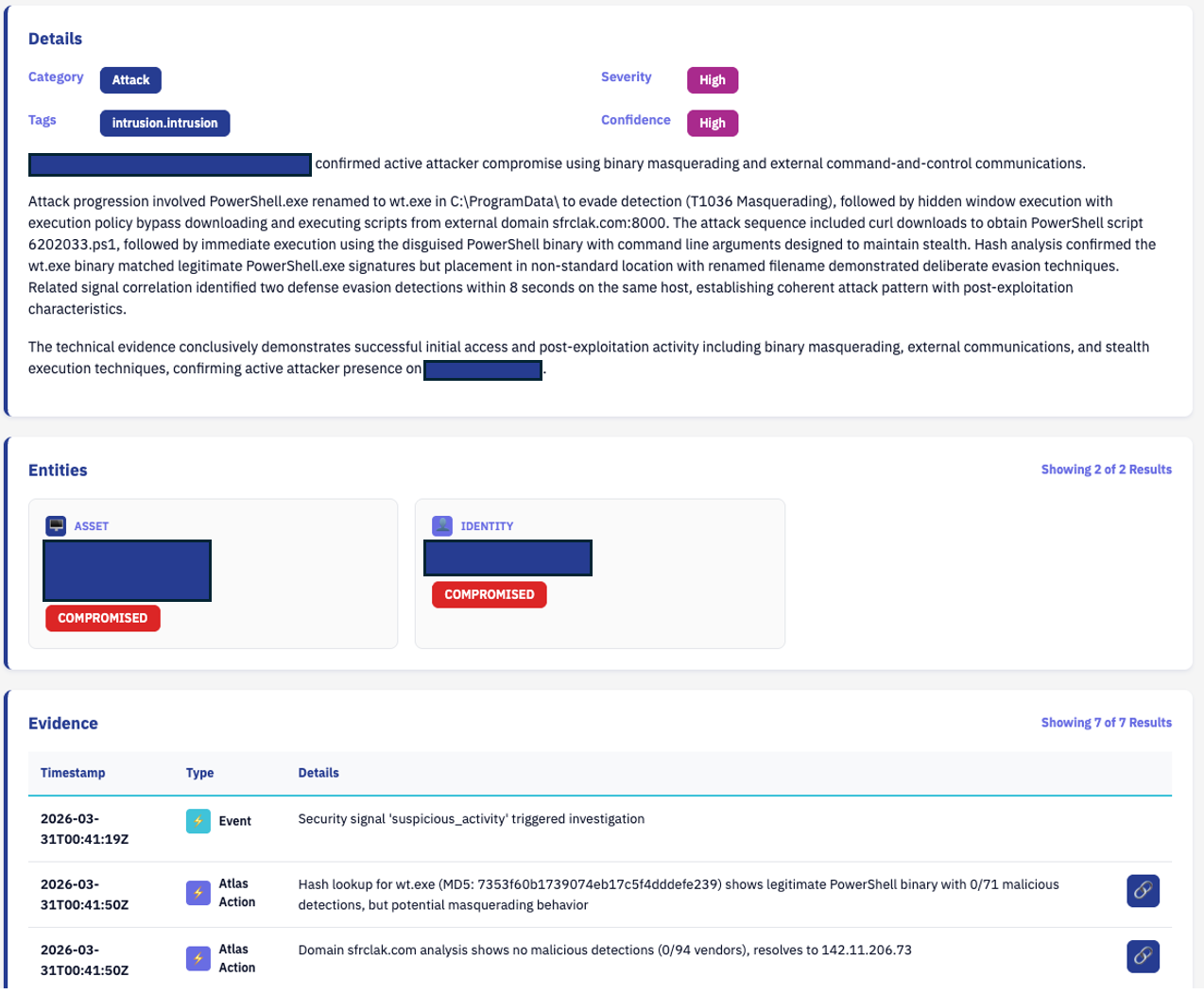
The figure below shows some of the automated triage associated with a Windows detection within the first 30 minutes of the supply chain attack. This triage correctly classified the payload delivery sequence as a high severity intrusion and recommended immediate containment and escalation of the host.
Following open-source reporting of the compromise, our TRU team worked with our SOC Cyber Analysts to validate existing cases and initiate our initial threat hunts on the evening of March 30th.
This was followed up with an in-depth threat hunting engagement across all customers the morning of March 31st. This hunt included known and suspected indicators of compromise and was repeated as new information emerged.
A total of 19 customers were affected between North America and EMEA regions. The majority of these infections occurred within the first hour, with some occurring minutes after the package update.
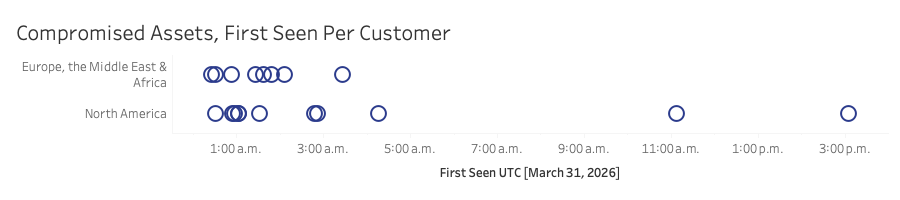
Given the ubiquitous use of Axios in web development, the software industry naturally bore the brunt of the impact. The geographic concentration of infections skewed outside of North America, a distribution correlated to the timing of the attack. The approximate three-hour window during which the compromised packages were live coincided with the start of the workday and automated CI/CD pipeline runs in EMEA, while North American teams were largely offline.
Overall, the observed impact would appear relatively small for such a popular npm package. This is thanks to existing endpoint detection of payload delivery mechanisms and quick response from the security community to quickly notify package maintainers and raise awareness of the issue.
We also noted connection issues with the C2, whether this was due to volume of requests or deliberate action by the adversary is unknown. As of writing follow-on activity from the RAT has not been identified, but analysis remains ongoing.
Final Thoughts
Open-source supply chain attacks remain a highly attractive vector for adversaries, as these campaigns abuse the inherent trust developers and organizations place in collaborative code-sharing communities. While foundational preventative measures, such as pinning exact package versions, sandboxing developer environments, and disabling automated dependency upgrades, are crucial first steps, they cannot entirely stop a sophisticated adversary from compromising a widely trusted package.
The incident emphasizes the necessity of defense-in-depth through continuous endpoint monitoring and active threat hunting – the core components of Managed Detection and Response (MDR). When preventative gates are inevitably bypassed, security teams must rely on catching the post-exploitation behavior on the host machine.
During the Axios attack, early detections did not originate from the npm registry, but from endpoint telemetry flagging the payload delivery mechanisms such as renamed PowerShell processes attempting to masquerade as wt.exe.
Ultimately, defending against advanced supply chain threats requires an "assume breach" mentality. Pairing strict dependency hygiene with continuous behavioral monitoring ensures that when a trusted open-source tool is weaponized, the resulting anomalous execution is identified and contained before threat actors can establish persistence or exfiltrate data.
Mitigation Recommendations
For detailed recommendations, read our latest security advisory and NPM Security best practices published by OWASP. In addition, implementing package release cooldowns can create a buffer during which fresh packages are inspected/scanned for tampering.
Here is how you would configure a 7-day (or equivalent) delay across the JavaScript ecosystem:
- npm (v11.10+): min-release-age=7 (measured in days).
- pnpm (v10.16+): minimumReleaseAge=10080 (measured in minutes).
- Yarn 4 (v4.10+): npmMinimalAgeGate: "7d" (uses a duration string).
- Bun (v1.3+): minimumReleaseAge=604800 (measured in seconds).
Exclusion lists such as minimumReleaseAgeExclude in pnpm or npmPreapprovedPackages in Yarn can allow fine tuning of these policies to exempt trusted internal packages.
Indicators of Compromise
To learn how your organization can build cyber resilience and prevent business disruption with eSentire’s Next Level MDR, connect with an eSentire Security Specialist now.
GET STARTEDABOUT THE AUTHOR

Spence Hutchinson Senior Manager, Threat Intelligence Research
As part of the broader Threat Response Unit, Spence is responsible for monitoring the evolving threat landscape and collaborating with TRU members to respond to ongoing threats. Throughout his tenure at eSentire, he has progressed through various analytical, training, and leadership roles, bringing extensive experience in threat research and security operations to the organization.