Business professionals search google for free office forms (invoices, questionnaires, and receipts) but get served a RAT
eSentire, a leading cybersecurity solutions provider, reported today that business professionals are currently being lured to hacker-controlled websites, hosted on Google Sites, and inadvertently installing a known, emerging Remote Access Trojan (RAT). eSentire has detected several incidents in the past week. The attack starts with the potential victim performing a search for business forms such as invoices, questionnaires, and receipts. Unlike the LinkedIn spearphishing campaign eSentire reported last week that utilized email and LinkedIn channels, this campaign lays long-standing traps for victims using Google search redirection and the drive-by- download method. Once the RAT is on the victim’s computer and activated, the threat actors can send commands and upload additional malware to the infected system, such as ransomware, a credential stealer, a banking trojan, or simply use the RAT as a foothold into the victim’s network.
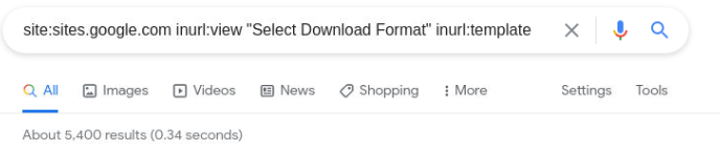
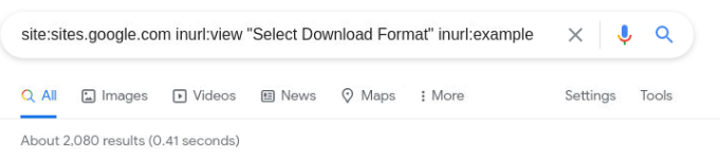
Upon attempting to download the alleged document template, users are redirected, unknowingly, to a malicious website where the RAT malware is hosted. eSentire’s Threat Response Unit (TRU) discovered over 100,000 unique web pages that contain popular business terms/particular keywords: template, invoice, receipt, questionnaire, and resume. In a precursory search, 70,000 unique web pages included the mention of either template or invoice. These common business terms serve as keywords for the threat actors’ search optimization strategy, convincing Google’s web crawler that the intended content meets conditions for a high PageRank score.
Once the target lands on a site controlled by the hacker, the page shows download buttons for the document template they were searching. When clicked, the business professional is redirected (unknowingly) to a malicious website which serves up an executable disguised as a pdf document or a word document. In the incident which eSentire investigated, when the executable (disguised as a pdf) was launched by the user, they simultaneously installed the SolarMarker RAT (also referred to as Yellow Cockatoo, Jupyter, and Polazert) and a complimentary copy of the Slim PDF reader application. Slim PDF is a legitimate application for reading pdfs. The pdf reader application is installed by the threat actors, either in an effort to convince the victim of the legitimacy of the document they were seeking or as a distraction from the installation of the RAT. As with any RAT, once SolarMarker is active, the threat actors can send commands and upload additional files to the infected system. The TRU has not yet observed actions-on-objectives following a SolarMarker infection, but suspect any number of possibilities, including ransomware, credential theft, fraud, or as a foothold into the victim networks for espionage or exfiltration operations.
Key Takeaways
- A Remote Access Trojan (RAT) with many names: Tracked as SolarMarker, Jupyter, Yellow Cockatoo and Polazert
- The threat actors behind SolarMarker have added Slim PDF to their list of decoy applications
- Switched from search redirection, via Shopify, to search redirection via Google Sites
Comment from Spence Hutchinson, Manager of Threat Intelligence for eSentire
“Security leaders and their teams need to know that the threat group behind SolarMarker has gone to a lot of effort to compromise business professionals, spreading a wide net and using many tactics to successfully disguise their traps,” said Spence Hutchinson, Manager of Threat Intelligence for eSentire. “For instance, the Solar Marker group has:
:
- Deployed over 100,000 web pages via Google Sites. The benefits of being hosted on Google’s infrastructure are several. First, Google is trusted by both security appliances and human eyes. Secondly, it probably doesn't hurt your PageRank score with Google to use Google’s infrastructure. The pages are also padded with generated text keywords, a tactic likely used to further influence search results.
- The threat actors have created tens of hundreds of web pages with popular business terms, such as invoice, statement, receipt, questionnaire, so that when a business professional is searching the Internet for a specific business template, then there is a chance that the top search results will include one of their malicious pages.
- The infection process relies on exploiting the user, not an application. The user simply executes a binary disguised as a PDF to infect the machine. This is an increasingly common trend with malware delivery, which speaks to the improved security of applications such as browsers that handle vulnerable code. Unfortunately, it reveals a glaring blindspot in controls which allow users to execute untrusted binaries or script files at will.
- The SolarMarker campaign utilizes a variety of decoy applications. Most recently, TRU observed that the Slim PDF reader software was the decoy being downloaded onto the victim’s computer. This serves as a distraction, as well as an additional element to help convince the victim that they are downloading a pdf.
“Another troubling aspect of this campaign is that the SolarMarker group has populated many of their malicious web pages with keywords relating to financial documents, e.g., statements, receipts, invoices, etc.,” continued Hutchinson.. “A financial cybercrime group would consider an employee, working in the finance department of a company, or an employee, working for a financial organization, a high value target. In fact, the SolarMarker incident which eSentire disrupted involved an employee of a financial management company. Once a remote access trojan (RAT) has been installed on a victim’s computer, the threat actors can upload additional malware to the device, such as a banking trojan, which could be used to hijack the online banking credentials of the organization. Or a credential stealer could be installed, which could be used to steal the employee’s email credentials, enabling the hackers to launch a business email compromise scheme. Unfortunately, once a RAT is comfortably installed, the potential fraud activities are numerous.”
How the Attack Works
The emerging RAT is written with the .NET software framework, and tracked as Jupyter, Yellow Cockatoo, SolarMarker, and now being tracked as Polazert on twitter [1]. SolarMarker was first observed by eSentire in early October 2020. The eSentire Threat Response Unit (TRU) tracks this threat as SolarMarker due to the observed tracking file dropped for host identification. Throughout October and November 2020, SolarMarker utilized docx2rtf.exe as a decoy to distract users as the .NET silently installed itself in the background. Red Canary reports SolarMarker changing this decoy application throughout the following months [4] using in September 2020 photodesigner7_x86-64.exe and Expert_PDF.exe in November 2020, while the TRU continued to see docx2rtf.exe. The TRU has now discovered that the SolarMarker group is using Slim PDF Reader. See Figure 1 and Figure 2.

Figure 1. The attack chain starts with a google search and ends in the installation of SolarMarker and lesser-known PDF viewer.

Figure 2: Process tree outlining the installation of SolarMarker. Note the Adobe icon on the installer file. The RAT, labeled (unknown), then goes on to install the decoy document and make malicious PowerShell calls.
SolarMarker captures victims via Google Search redirect. Often, clients are looking for a free version or template of a document. In the latest incident observed by TRU, the victim, who works in the financial industry, was redirected to a Google Sites page controlled by the threat actor with an embedded download button. The download button, hosted at passiondiamond[.]site, is easy to customize. The TRU team was able to generate a document named “this is a test” for download (Figure 3). Note the search redirect content (see Figure 4) populated on the malicious web page just below the download buttons in Figure 3.

Figure 3: The Download button that is embedded in the Google Site

Figure 4: The search redirect content populated on the malicious web page just below the download buttons in figure 3.

Figure 5: Examining the source of the embedded button page reveals a link to a .tk domain and icon sources
The decoy program, Slim PDF, serves as an important visual cue for potential victims of SolarMarker but also helps to lower suspicion of malicious intent. The attached screenshot (Figure 6) is from the Slim PDF website

Figure 6: Screenshot from the Slim PDF reader website
Evolution of Distribution Method
eSentire's TRU first saw SolarMarker utilizing Shopify for its search redirection method in October 2020. In that case, the redirection infrastructure was embedded in a hosted PDF that provided links to the threat actor’s maliciously controlled infrastructure where the RAT (and its decoy payloads) is hosted. In 2021, the redirection method shifted to Google Sites.
The redirection method for Shopify was highlighted by Security Magic [5] who also mentioned the usage of Google Sites. To capture search results, the threat actors loaded the redirection content with keywords. In the case of Shopify, the keywords were hidden as white text at the bottom of the PDF (Figure 7). In recent attacks, however, Google Sites is being leveraged with an embedded download button (Figure 3) that leads to attacker-controlled infrastructure. As with the Shopify PDF, a block of text with keywords is included. In the case of Google Sites, the keyword content is placed directly in the site, below the landing button and some white space (Figure 4).

Figure 7: Highlighting the second page of the Shopify-hosted PDF reveals the hidden text used to rank high in Google results
Redirection
The redirection infrastructure passes through a series of .tk TLDs before landing on the final .ml TLD domain. See Figure 8. Upon visiting the infrastructure with a VM, no such redirects are experienced. Upon inspecting the source code of the embedded download button at passiondiamond.site, researchers found an entirely different .tk domain, indicating a possibility that these redirect pathways are dynamic and can be changed for either operational security or delivery efficacy. It’s possible that any number of checks are being performed on the visiting browser and operating system to ensure they are being operated by victims, not security researchers.

Figure 8: SolarMarker’s redirect path from the search result to the final payload site
Four Names, One Malware
[1] Mar 09, 2021 - https://twitter.com/JAMESWT_MHT
Being tracked as #Polazert
[2] Feb 08, 2021 - https://www.crowdstrike.com/blog/solarmarker-backdoor-technical-analysis/
Google Sites mentioned
Infection Chain Shown
Detailed Reversing / Snippets
[3] Dec 12, 2020 - http://security5magics.blogspot.com/2020/12/tracking-jupyter-malware.html
Shows Shopify Method
Google Sites mentioned
[4] Dec 04, 2020 - https://redcanary.com/blog/yellow-cockatoo/
Overview of Decoys used
[5] Nov 12, 2020 - https://blog.morphisec.com/jupyter-infostealer-backdoor-introduction
First Public Report on SolarMarker
SolarMarker Incident Dissection:
- Victim uses Google to search for an ethics questionnaire
- Business professional visits sites.google.com (Google’s generic site hosting offering)
- Web Page is controlled by threat actor
- Includes content from passiondiamond.site
- Can put any arbitrary text in passiondiamond component
- When the victim downloads, several v6 IPs are contacted to fetch the payload disguised as a PDF.
- Mostly .tk T
- A single .ml TLD
- Client detonates questionnaire from Downloads folder
- Opens a lesser- known free PDF reader
- Installs the core .NET functionality of the RAT as .tmp executable
- RAT calls powershell
- PowerShell Beacons to potential C2
- Last updated: 2021-03-23 RIPE Network Coordination Centre
An example of the number of web pages, where the body copy of the page, contains the following search terms: excel, invoice, template.




Web pages in which the alleged document title included the search terms: template, invoice, statement, excel, and hansard (a Canadian legal document).






For more information about this threat and how to protect against it go to https://www.esentire.com/get-started